-
Products
Individual
Access work laptop and gaming computer from PC/Mac/phone from anywhere for free
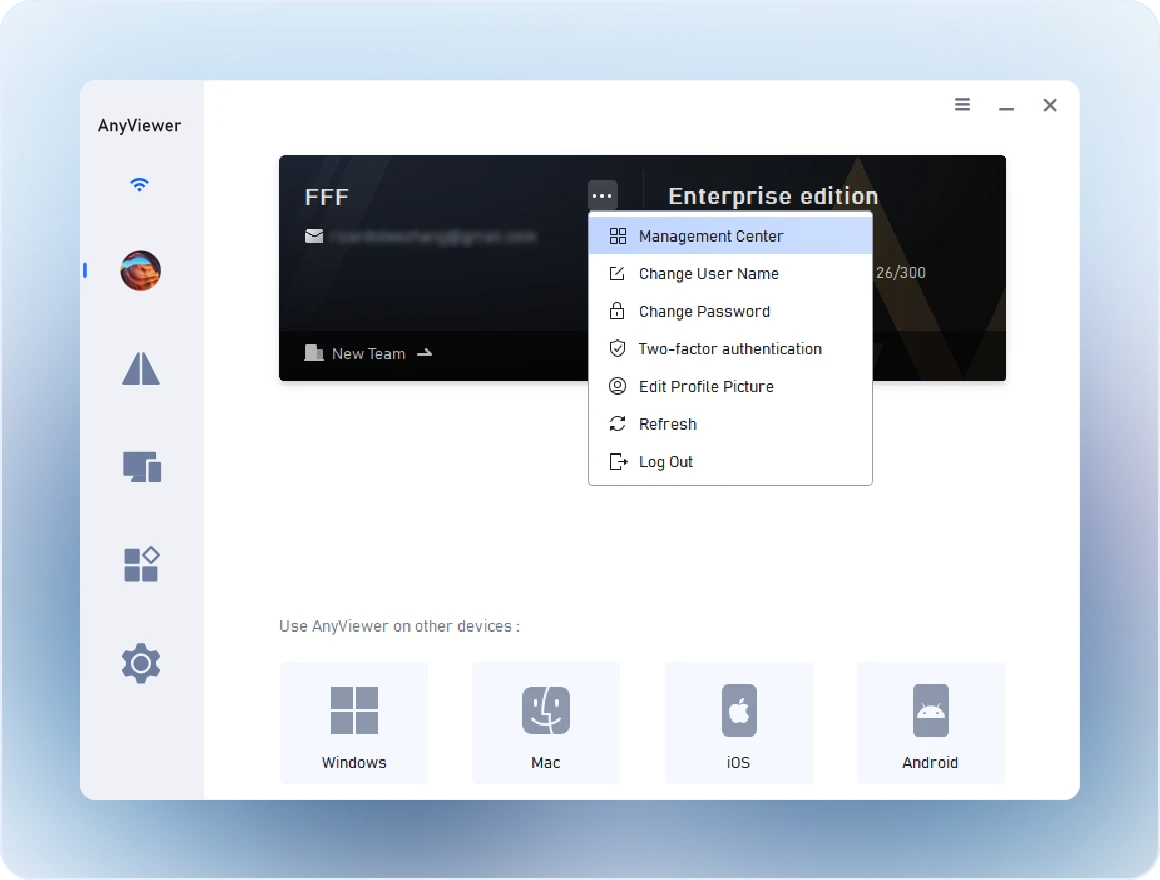
Business
All-in-one secure remote work and support for teams, organizations, and enterprises
Platforms
- Solutions
-
Features
-
Unattended Remote Access
Access remote devices without permission.
-
Screen Mirroring
Mirror screens wirelessly across devices.
-
File Transfer
Move files between devices quickly.
-
Privacy Mode
Invisible remote access with a black screen.
-
Screen Wall
Monitor multiple screens simultaneously.
-
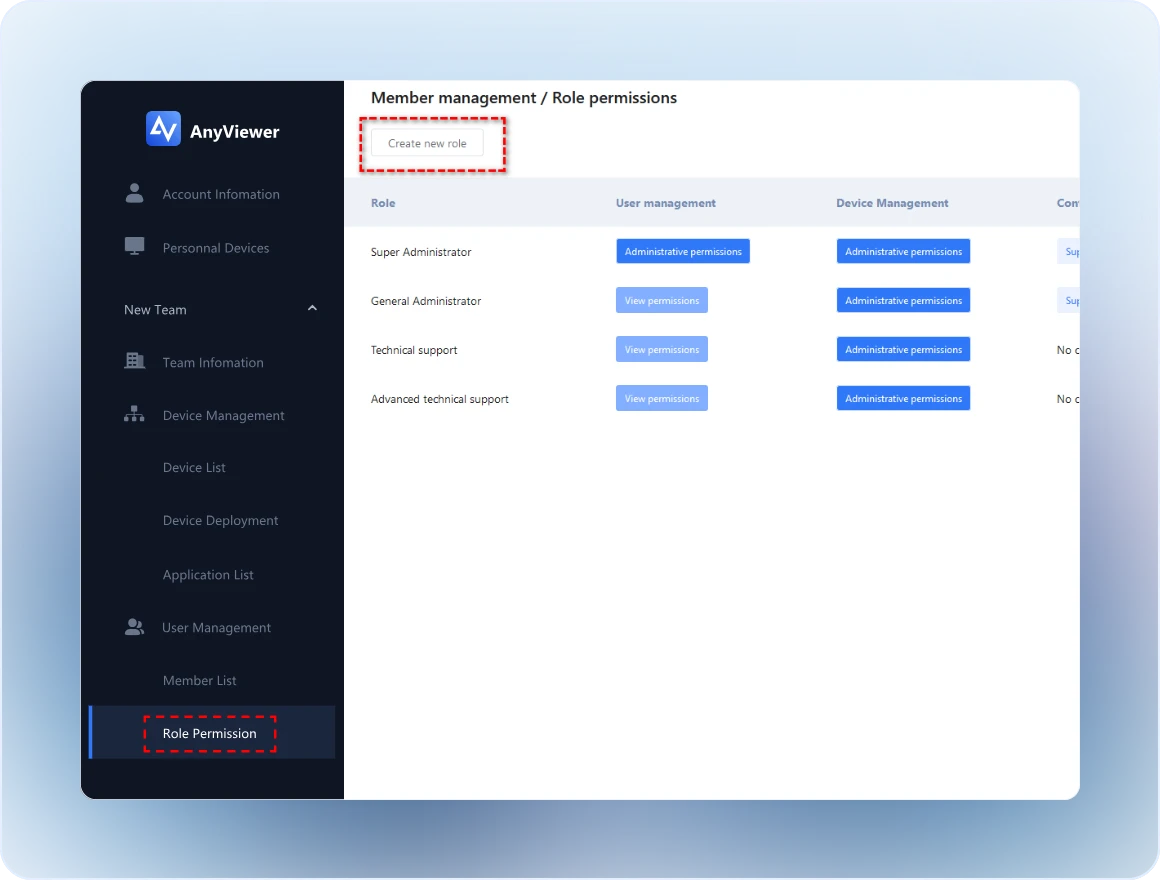
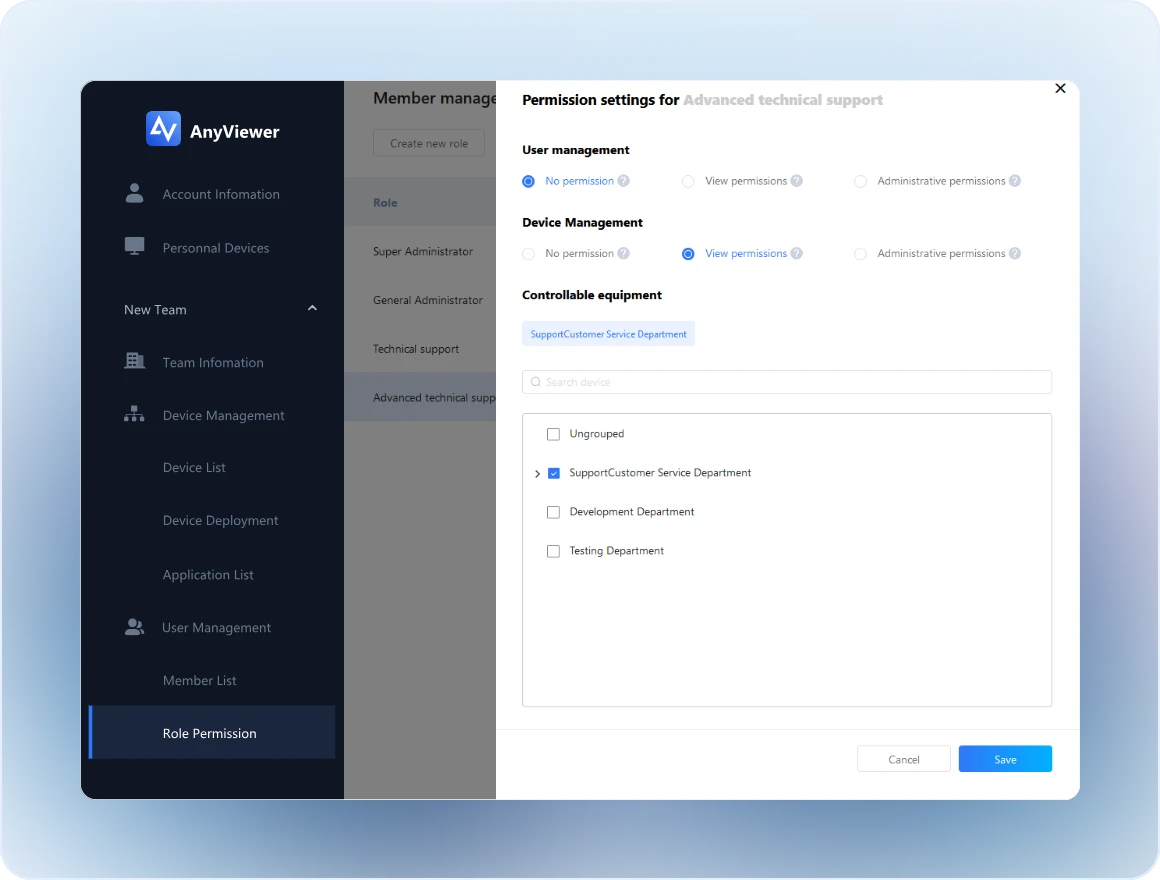
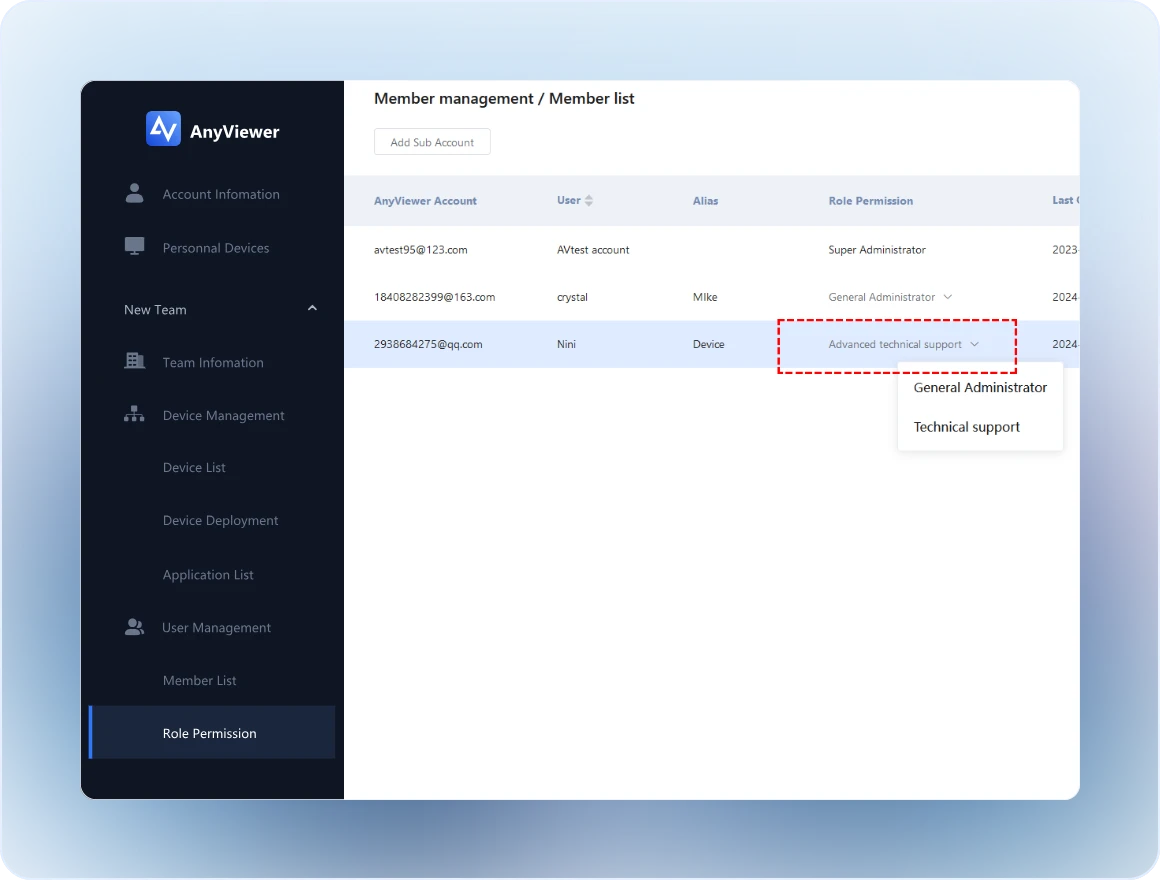
Role Permission Management
Manage user access with flexible permissions.
-
- Pricing
- Company